About LoRaWAN
LoRaWAN (or LoRa for short) is a LPWAN (“Low-Power Wide Area Network”) technology. The radio technology used is nifty and ensures you can send data across fairly large distances with very little transmission power used.
LoRa operates in what is known as the “ISM” (aka “Industry Science Medical”) band, a part of the radio spectrum that is unlicensed. This does not mean that you can use it in any way you desire, there’s a limit on how much power you can use and for how long you can transmit at a time. This is known as the “duty cycle”. The duty cycle for LoRa is between 1% and 0.1%, depending on what bit rate you are sending on.
A bird’s eye view of LoRaWAN
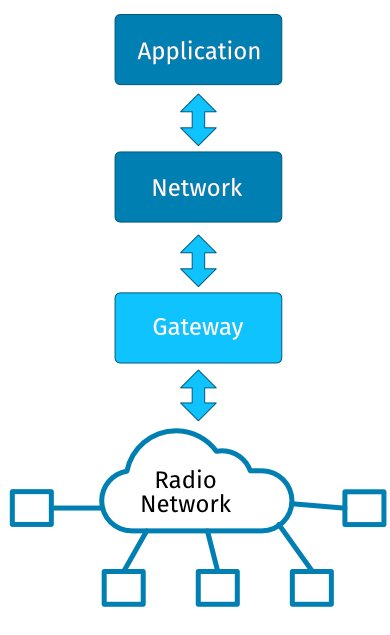
A LoRaWAN network consists of gateways, networks, applications and devices. The devices sends radio packets to the gateways which is part of a network. A network consists of applications which again consists of zero or more devices. The networks and applications are ususally abstractions in the backend service.
The devices communicate with one or more gateways via radio. Each packet is fairly short, usually no more than a few tens of bytes. The packets are picked up by one or more of the gateways and the devices goes to sleep, typically for a second before it starts listening for a response from the gateway. If the gateway has data that is scheduled for the device it will send the data to the device. Once this is completed the device goes into sleep again until it has more data and it is allowed to send according to the duty cycle.
The gateways (or concentrator) decodes the radio packet into a small buffer and forwards the buffer to the LoRa backend. The LoRa backend keeps track of all of the gateways and networks and determines which network the packet belongs to, if the devices is known by the network the data is passed on to the application that the device belongs to. If there’s data scheduled for the device it will go back through the receiving gateway and out to the device.
Bandwidth
Since the packets sent by the devices are fairly small and the devices only send one packet every five minutes you won’t get a lot of data to and from the devices so the typical use case scenarios are devices that send small amounts of data infrequent, typically only a few times every hour or day.
Range
The range of device can be quite impressive. A simple wire antenna is sufficient to reach gateways several kilometers away. There’s no magic here; if you sit in a metal cage you won’t get good coverage and the radio waves won’t go through walls or metal but the protocol itself makes it possible to pick up even weak transmissions. Field experiments show that a LoRa device can get several kilometers of range in urban environments and even better range with line of sight, upwards of 20 kilometers or more. Radio waves are weird so you can get good coverage in seemingly impossible places but next to nothing in other places.
Getting a gateway
If you can’t get any coverage where you live or in your part of town – fear not. A LoRa gateway is relatively cheap (€100 and up) and it requires little maintenance. You can run a gateway on dedicated hardware or on a Raspberry Pi.
Security
All of the data that is transmitted between devices and applications in a LoRaWAN network is encrypted with AES-128. There’s two encryption keys in use, a network session key and an application session key. Both keys are unique for the devices and is used for network-level messages and application payloads respectively. If you use some clever key management you can keep the application/device payload a secret shared only by the application and the device without the network (or gateway) operator knowing what the payload is.
Networks
A network in LoRaWAN works similarly to a mobile phone network. Multiple networks can operate in the same area and multiple networks can operate out of the same gateway. The biggest difference is that devices in LoRaWAN can’t jump from network to network since a device is connected to an application which can only be a member of a single network.
Applications
An application in LoRaWAN is simply a collection of devices that runs on a given network. A device cannot be part of more than one application and a device can’t exist without an application.
Relevant links:
- The LoRa Alliance: https://lora-alliance.org
- The Things Network: https://www.thethingsnetwork.org
- Understanding the Limits of LoRaWAN (Adelantado, Vilajosana et al, IEEE magazine january 2017): https://arxiv.org/pdf/1607.08011.pdf